CURRENT AFFAIRS 07-01-2022
Daily Current Affairs – Topics
- EWS Income Criteria
- Dams Safety in India
- Securing Internet of Things
- POSH Act
- Jagannath Temple Act, 1954
1. EWS Income Criteria
#GS2- Government Policies & Interventions
Context
- A committee set up by the Ministry of Social Justice and Empowerment recently delivered a report on the income criteria used to determine who should be included in the Economically Weaker Sections (EWS). The report has been accepted by the government, which has filed an affidavit in the Supreme Court.
In depth Information:
What suggestions did the panel make?
- A fine balance of 8 lakhs:
- The Rs 8 lakh criterion achieved a “tight balance” between over-inclusion and inclusion errors, according to the committee, and was judged to be a “acceptable” threshold for determining EWS in order to extend reservation in admissions and jobs.
- Given that the existing effective income tax exemption level for individuals is roughly Rs 8 lakh, the committee believes that a gross annual income ceiling of Rs 8 lakh for the entire family would be reasonable for EWS inclusion.
- Notion of OBC Criteria Emulation Was Rejected:
- It refuted the claim that the Centre “mechanically adopted” Rs 8 lakh as a figure because it was also used for the creamy layer cut-off for OBCs (Other Backward Classes).
- For EWS, the income criterion is more stringent:
- To begin with, the EWS criteria apply to the financial year preceding the application year, but the income criterion for the creamy layer in the OBC category applies to gross yearly income for three consecutive years.
- Secondly, in case of OBC creamy layer, income from salaries, agriculture and traditional craft professions are excluded from the consideration but the Rs 8 lakh threshold for EWS includes all sources, including farming.
- As a result, while having the same cut-off number, their compositions are dissimilar, and the two cannot be compared.
- Uniform Income Threshold Backed by SC:
- The Supreme Court has affirmed the value of a uniform income-based threshold, which can be implemented across the country as a matter of economic and social policy.
Recommendations:
- In the case of educational institution admissions, the sudden adoption of new criteria would inevitably and necessarily delay the process by several months, with a cascading effect on all future admissions and educational activities/teaching/examinations that are bound by various statutory or judicial time constraints.
- However, a person whose family owns 5 acres or more of agricultural property may be excluded from EWS regardless of income. The residential asset condition may be eliminated entirely.
- The residential asset criteria were dropped entirely, but the five-acre agricultural plot criteria were kept.
- A three-year feedback loop cycle might be used to track the real-world results of these criteria and then alter them in the future.
- Data sharing and information technology should be utilised more frequently to verify income and assets, as well as to better targeting for EWS reservations and other government programmes.
- Existing and ongoing criteria in any ongoing process where an EWS reservation is available should be maintained, and the criteria specified in this report should be implemented beginning with the next advertisement/admission cycle.
2. Dams Safety in India
#GS3 -Infrastructure
Context
- According to a new assessment from the Comptroller and Auditor General of India (CAG), the Gandhi Sagar Dam on the Chambal River in Madhya Pradesh is in desperate need of repair.
In depth information
Key Findings
- According to a report released by the Comptroller and Auditor General of India (CAG) on December 23, 2021, the dam has been plagued by serious difficulties for years, including a lack of regular checkups, non-functional instruments, and clogged drains.
- The dam inspection report classified Gandhi Sagar as Category II.
- Dams in Category I have serious flaws that could lead to complete or partial failure and require immediate correction. Category II refers to those who have mild to medium flaws that are fixable but require quick treatment.
- There is one dam in Category I, according to the CAG assessment, although it is not named. There were as many as 27 minor MP dams in Category II.
- In India, there is a pressing need for dam safety.
- There are about 5,200 major dams in the country. While some dams are located within a state, they are owned by another state and are not responsible for their upkeep.
- There are thousands of other small and medium dams throughout the country in addition to these. There are 293 dams older than 100 years and 1,041 dams older than 50 years among the total major dams.
- The safety and maintenance of these enormous numbers of dams are a source for worry in the absence of a sufficient regulatory framework.
- The Dam Safety Bill of 2019 ensures that all dams in the country are properly monitored, inspected, operated, and maintained.
Ahead of Schedule
The following functions relating to dam safety must be strengthened:
- For current and future dams, new acceptance criteria must be developed.
- Dam safety reviews and MIS, as well as Dam registries and online databases, are available.
- Dam safety technology acquisition and dissemination to state governments and organisations.
- Dam break studies, glacial break studies, and emergency action plans are all things that need to be done.
- Dam Safety Legislation is being monitored for implementation.
- Modernization of technology for the efficient repair of troubled dams
- Set up State and Central Dam Safety Services through legislation.
| About Gandhi Sagar Dam
? The Gandhi Sagar Dam is located in Gujarat, India. ? In 1960, the Gandhi Sagar Dam was built to provide potable water to many Rajasthan regions as well as create 115 megawatts of electricity. In recent years, it has been broken multiple times, producing floods in downstream neighbourhoods. ? Sheopur, Morena, and Bhind, three districts in the state, with a combined population of 4.35 million (as of the 2011 Census), are downstream of the dam. ? The Gandhi Sagar Dam was one of the few national-level dams to be installed, but many of the devices have been inoperable for years, according to the CAG study. ? According to the CAG, the state dam safety organisation (SDSO), which is responsible for its upkeep, did not follow the recommendations of the Central Water Commission (CWC) and the Dam Safety Inspection Panel (DSIP) on remedial measures.
|
3. Securing Internet of Things
#GS3-Technology
Context
- Telecommunication Engineering Centre (TEC), under the Department of Telecommunications, Ministry of Communications, recently produced a study titled “Code of Practice for Securing Consumer Internet of Things(IoT)” in order to safeguard Consumer Internet of Things (IoT) devices.
- These rules will aid in the security and management of consumer IoT devices and ecosystems.
In depth information
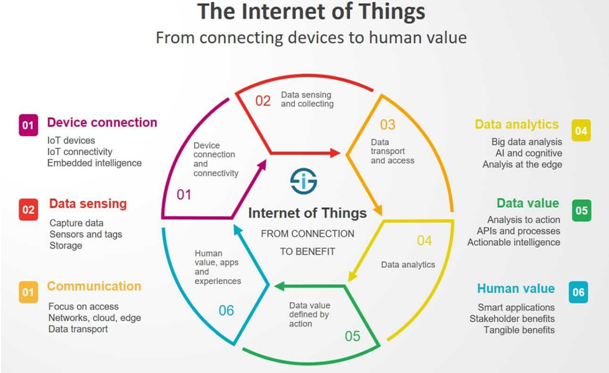
The Internet of Things (IoT) is a term that refer
- It’s a computing concept that explains the idea of ordinary physical things being connected to the internet and being able to recognise themselves in the presence of other devices.
- One of the World’s Fastest Growing Technologies: It is one of the world’s fastest growing technologies, with significant benefits for society, industry, and consumers.
- Using linked devices, the Internet of Things is being utilised to develop smart infrastructure in numerous verticals such as power, automotive, safety and surveillance, remote health management, agriculture, smart homes and smart cities, and so on.
- A smart device is a context-aware electronic gadget capable of autonomous computing and data exchange via wire or wireless connections with other devices.
- Supplementary Technologies: Recent advancements in numerous technologies, including as sensors, communication technologies (both cellular and non-cellular), artificial intelligence/machine learning, cloud/edge computing, and so on, have benefited IoT.
- By 2025, it is estimated that there will be roughly 11.4 billion consumer IoT devices and 13.3 billion commercial IoT devices worldwide, with consumer IoT devices accounting for nearly 45 percent of all IoT devices.
- The global IoT security market is predicted to increase from USD 8.2 billion in 2018 to USD 35.2 billion by 2023, according to a market research analysis released by Markets and Markets.
Guidelines Are Required:
- Expected Growth:
- With the expected growth of IoT devices, it’s critical to make sure that IoT endpoints meet safety and security requirements.
- Cyber-Security Attack:
- Hacking of everyday devices/networks will cause harm to businesses, organisations, nations, and, most importantly, people.
- As a result, end-to-end security of the IoT ecosystem, from devices to applications, is critical.
- End-to-end security for connected IoT devices is critical for market success; without security, IoT would perish.
- Concerns about privacy:
- In this data-driven future, there is rising concern about the possibility of increased government surveillance and encroachment on civil liberties, as well as the suppression of dissent or marginalised communities.
Cybersecurity Attack Consequences:The following are some of the possible outcomes of such attacks:
- Critical services/infrastructure are disrupted and unavailable.
- Invasion of one’s privacy.
- Death, money, time, property, health, and relationships are all examples of losses.
- Civil unrest, as well as national-scale disruptions.
Consumer IoT security guidelines:
- No universal default passwords:
- During device provisioning, every IoT device default passwords must be unique per device and/or require the user to specify a password that meets best practises.
- Implement a method for managing vulnerability reports:
- As part of a vulnerability disclosure policy, IoT developers should establish a dedicated public point of contact.
- Keep your software up to date:
- IoT device software should be updateable in a secure manner.
- Securely store important security parameters:
- IoT devices may be required to store sensitive security parameters such as keys and credentials, certificates, device identity, and so on, which are necessary for the device’s secure operation.
- Securely communicate:
- Security-sensitive data, including any remote administration and control, should be encrypted in transit, in accordance with the technology’s features and the device’s intended use.
- Reduce the number of attack surfaces exposed:
- Devices and services should follow the ‘principle of least privilege.’
- According to the Principle of Least Privilege, a subject should be granted only the privileges necessary to fulfil its mission.
- Ensure that personal data is kept safe:
- If the device gathers or transmits personal information, it should be kept safe.
- Make systems resilient to outages:
- Where their usage or other depending systems require it, resilience should be included into IoT devices and services.
Next Steps
- Addressing Data Security Concerns: While IoT technology certainly provides tremendous benefits to citizens around the world, it also poses a serious threat to privacy.
- This data security problem will have to be addressed, and IoT device manufacturers will have to earn and maintain consumer trust in their products.
- The Data Protection Bill, 2019, is a step in the right way in this regard.
- Global Deliberation is Required: Legislators, device manufacturers, and law enforcement agencies from all around the world should collaborate to figure out how to reap the benefits of IoT while minimising hazards.
4. POSH Act
#GS2- Judiciary
Context
- The Supreme Court has upheld the Bombay High Court’s contentious guidelines effectively prohibiting the media from reporting on allegations of sexual harassment at work, claiming that the directives are a “death blow” to freedom of speech and expression.
In depth information
- The G.S. Patel rules were created by Justice G.S. Patel of the High Court, presumably to protect the names of the parties in a POSH Act case.
What were the Rules of Engagement?
- No Mention:
- In any court order, neither the names of the parties nor their personally identifying information should be mentioned.
- Not to be uploaded:
- Orders and merits judgements are not to be uploaded. All instructions and judgements will be given in secret, in chamber or in camera.
- The entire record will be kept sealed and will not be released to anybody without a court order. New filings must also be sealed.
- All hearings will take place in camera or in chamber. There isn’t an online option. It’s all about physical looks. The court’s support personnel is required to leave.
- The orders will not be released in the public domain unless there is a specific court order. Only an anonymized version of the order will be made public at most.
- Both sides, parties, and advocates are barred from leaking the contents of any order or judgement to the media. Non-disclosure agreements must be signed by witnesses.
- Contempt of court is defined as any violation of the rules.
Problems and Obstacles
- It contains a blanket ban on parties and advocates sharing records with the media, including orders and judgments.
- In such situations, orders will not be posted on a court’s website, and the press will not report on a ruling issued under the Act unless the court gives permission.
- Article 19:
- It is a “death blow” to Article 19’s guarantee of freedom of speech and expression.
- Informational right:
- Any restriction on people’s right to know genuine and accurate facts is a violation of their right to information.
- Dissuade survivors from accessing the courts:
- The HC order could have a “ripple effect,” discouraging survivors from approaching the courts and setting a dangerous precedent for trial cases.
- It will legitimise disproportionate protection for sexual offenders, in direct contravention of the norms of open court, natural justice, and survivors’ fundamental rights.
- The HC order is in violation of the ideals of open court contained in the Swapnil Tripathi case.
- Termination:
- In a lawsuit for compensation for unjust and retaliatory termination, such an order cannot be made.
- To silence women’s voices:
- it will aid “powerful companies in their efforts to silence women’s voices.”
Next Steps
- A well-informed citizenry is better able to govern itself: Only if it interferes with the administration of justice may the right to free expression be curtailed.
- Public discourse: When it comes to issues of social justice and women’s empowerment, public discourse is critical in determining the form of legal entitlements provided to women.
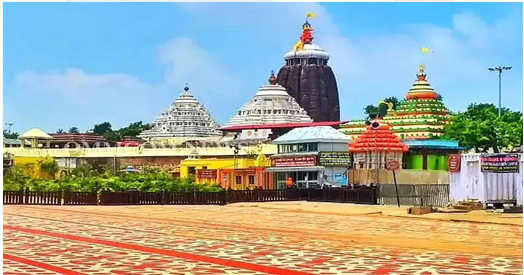
5. Jagannath Temple Act, 1954
#GS1-Temple Architecture
Context
- The Odisha state cabinet has authorised revisions to the Sri Jagannath Temple Act of 1954, which is a historic decision.
In depth information
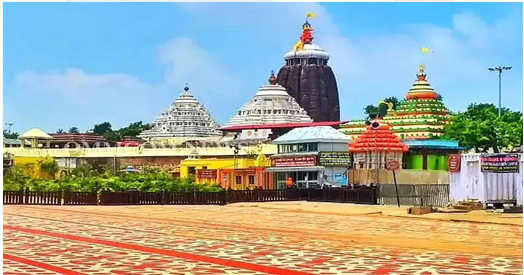
- About: In the year 1806, the British administration imposed instructions for the operation of the Jagannath temple, which the colonial rulers dubbed the Juggernaut temple.
- Pilgrims who visited the temple were required to pay taxes under these rules.
- Senior priests at the temple were to be appointed by the British administration.
- After three years, the temple’s management responsibilities were transferred to the King of Khordha, though the colonial authority retained considerable influence.
- The Jagannath Temple Act was passed in 1952 when India got independence, and it went into effect in 1954.
- The Act covers the temple’s land rights, the sevayat’s (priests’) duties, the Shri Jagannath Temple Managing Committee’s administrative authorities, the Raja of Puri’s rights and privileges, and other people involved in the temple’s management and administration.
Amendments made recently:
- The authority to sell and lease land in the name of Jagannath temple will now be assigned to the temple management and concerned officials.
- Unlike in the past, the process will not require state government approval.
- According to Section 16 (2) of the act, no immovable property taken into possession by the temple committee may be leased, mortgaged, sold, or otherwise transferred unless the State Government has given its prior approval.
Our Courses
Watch Our Videos on YouTube